Tabela de Conteúdos
![]()
2.3.2 Ssh Server
Instlalation
root@server:~# aptitude install openssh-server openssh-client
Configuration
The SSH server configuration is stored in /etc/ssh/sshd_config.
The netword address and port where ssh server accepts connections can be configured. Our server will only accept connections connections to address 192.168.1.100 and port22 and honoring SSH protocol version 2:
- /etc/ssh/sshd_config
# Package generated configuration file # See the sshd_config(5) manpage for details # What ports, IPs and protocols we listen for Port 22 # Use these options to restrict which interfaces/protocols sshd will bind to #ListenAddress :: #ListenAddress 0.0.0.0 ListenAddress 192.168.1.100 Protocol 2 #[...]
For safety reasons, root logins will be disabled. This will prevent brute force attacks to root password:
- /etc/ssh/sshd_config
#[...] # Authentication: LoginGraceTime 120 PermitRootLogin no StrictModes yes #[...]
Also, no logins with empty passwords are allowed:
- /etc/ssh/sshd_config
#[...] # To enable empty passwords, change to yes (NOT RECOMMENDED) PermitEmptyPasswords no #[...]
Restart the service:
root@server:~# /etc/init.d/ssh restart
Verification
Linux Clients
It should now be possible to establish a ssh connection to our server:
The first time you login into a remote server you will be warned that the identity of the host could not be established:
fribeiro@laptop:~$ ssh 192.168.1.100 The authenticity of host '192.168.1.100 (192.168.1.100)' can't be established. RSA key fingerprint is ee:16:b0:c9:1b:ef:b4:64:e1:86:80:f4:36:9f:08:03. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.1.100' (RSA) to the list of known hosts. fribeiro@192.168.1.100's password: Linux server 2.6.32-5-amd64 #1 SMP Fri Oct 15 00:56:30 UTC 2010 x86_64 The programs included with the Debian GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. fribeiro@server:~$ logout Connection to 192.168.1.100 closed. fribeiro@laptop:~$
root logins are not accepted:
fribeiro@laptop:~$ ssh -l root 192.168.1.100 root@192.168.1.100's password: Permission denied, please try again. root@192.168.1.100's password: Permission denied, please try again. root@192.168.1.100's password: Permission denied (publickey,password).
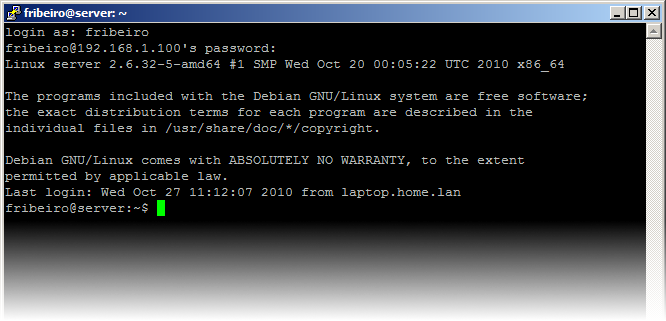
Windows Clients
An excellent choice as a windows based SH client is PuTTY:
Becoming root
Because root logins are disabled, to become root in a ssh session, you must login as a 'regular' unprivileged user and then use su command to change your identity to root:
fribeiro@laptop:~$ ssh 192.168.1.100 fribeiro@192.168.1.100's password: Linux server 2.6.32-5-amd64 #1 SMP Fri Oct 15 00:56:30 UTC 2010 x86_64 The programs included with the Debian GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Wed Oct 27 11:01:21 2010 from laptop.home.lan fribeiro@server:~$ su - root Password: root@server:~#
References
- Debian Reference, 6.9. The remote access server and utility (SSH) (http://www.debian.org/doc/manuals/reference/ch06.en.html#_the_remote_access_server_and_utility_ssh
- OpenSSH (http://www.openssh.com/)